Top listed Threats & Risks to Cloud Services and how to avoid them?

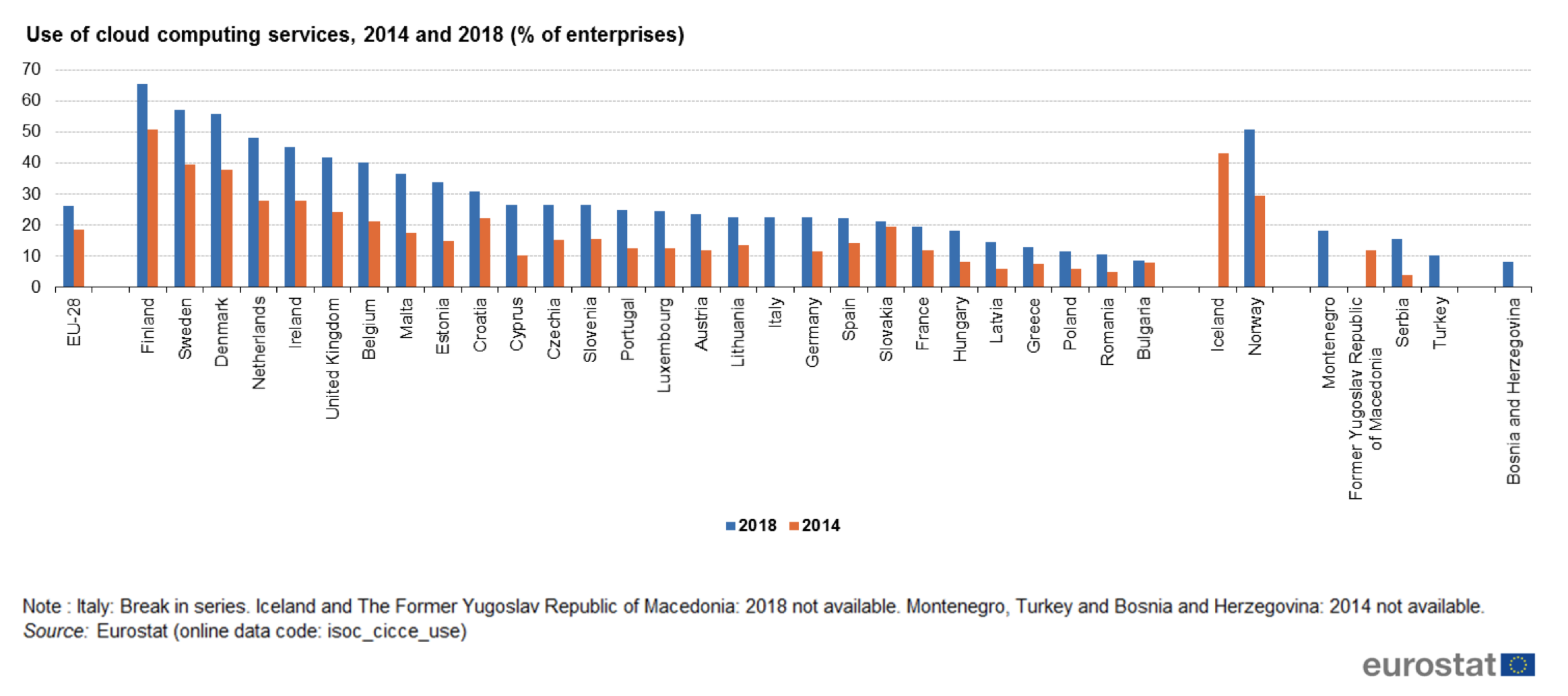
Many businesses have already shifted their workloads to the cloud in an effort to increase efficiency and streamline workloads. According to the Flexera 2021 State of the Cloud Report, roughly 90% of enterprises anticipate cloud usage will expand even further as a result of COVID-19. Even though the cloud has a lot of benefits to offer, it’s very important to highlight all the risks involved. A lack of understanding of cloud vulnerabilities and misconfigurations of cloud security settings can easily lead to cloud data breaches, as the enormous amounts of data, that cloud servers host, make them an attractive target for hacker attacks. Threats to cloud environments are in many ways related to the threats via in-house enterprise networks. Pierre Gronau, the cloud security expert, reveals twelve risks and expresses specific recommendations to minimize the risk of abuse and externally enforced data loss.
Data Breach
A company is responsible for the protection of its data. In the case of a data breach that has become public, preliminary investigations, lawsuits, legal disputes, and the resulting loss of revenue, as well as a sustained loss of reputation, are threatened. Therefore, when choosing the cloud provider, special attention must be paid to physical and digital security controls.
Insufficient identity, credential, and access management
Data breaches and other attacks often result from lax authentication, weak passwords, and poor key or certificate management. IT departments have to weigh the benefits and risks in a balancing act: on one hand, there is the efficiency of centralizing identity. On the other hand waits for the danger that such a valuable central directory, the repository, represents a worthwhile target. Businesses should rely on multifactor authentication such as time passwords, phone-based authentication, and SmartCard access protection for greater security.
Unsafe interfaces
IT teams use interfaces and APIs to manage and interact with cloud services. This includes services that provide cloud provisioning, management, and monitoring. These APIs and interfaces are typically the most exposed part of a system because they are usually openly accessible over the Internet. The Cloud Security Alliance (CSA) recommends security-oriented code reviews and rigorous penetration testing. Useful in this context are API security components such as authentication, access control, and activity monitoring.
System vulnerabilities
Organizations share storage, databases, and other resources in the immediate locale area, creating new attack surfaces and the potential for exploitable errors. However, IT teams can ease attacks on such system vulnerabilities with basic IT processes. One of these processes is speedy fixing. Change-control processes that address emergency patches ensure that all corrective actions are properly documented and reviewed by technical teams. The optimal time window for this is four hours.
Account takeover
Phishing, fraud, and software exploits are still successful. Cloud services add a new dimension to these threats as attackers enforce damaging activity, manipulate transactions, and change data. To avoid this, companies should monitor all accounts, including service accounts, to trace each transaction back to its human owner. The key is to protect each account’s credentials from theft.
Malicious insiders
The insider threat has many faces: a current or former employee, a system administrator, contractor, or business partner. The range of malicious actions ranges from forced data abuse to data theft. We can say that the game publisher Zynga learned a lot via his previous experience. In November 2016, employees copied a large amount of player data from the company’s Google Drive account to a USB stick. Goal: They wanted to join the competition after leaving the company. Systems that depend solely on the security of the cloud service provider are at the greatest risk. Protection provides effective logging as well as monitoring and auditing of administrator activities. To minimize the burden of access, organizations should work with encryption processes and keys, as well as quantitatively minimize access to systems.
Advanced persistent threats
The CSA identifies advanced persistent threats (APTs) as parasitic forms of attack. APTs infiltrate systems and then secretly exfiltrate data and intellectual property for extended periods of time. Possible entry points include direct attacks, targeted e-mail fraud, spear phishing, and attacks via USB drivers. To be prepared, IT departments need to keep abreast of the latest attacks. In addition, regularly updated awareness programs ensure that users remain alert and less susceptible to letting a parasite into the web.
Data loss
Reports of persistent data loss due to cloud provider errors have become extremely rare. Hackers, however, are still showing off their active side by permanently deleting corporate and data center cloud data to damage the company’s reputation. Here cloud providers recommend the distribution of data and applications, daily backup, and offsite storage. Compliance policies often dictate how long companies need to retain audit records and other documents – the loss of this data can have serious regulatory consequences.
Insufficient due diligence
Organizations that use cloud services without fully understanding these and the associated risks must accept commercial, technical, legal, and compliance risks. If development teams are not familiar with cloud technologies, operational and architectural issues can arise. At this point, developers must conduct a comprehensive due diligence process to assess the risks associated with their cloud services. The duty of care in the cloud environment is always and especially valid for cloud migrations, consolidation, and outsourcing.
Abuse and harmful use of cloud services
Hackers can use cloud services to support their criminal activities. An example is the use of cloud computing resources to crack an encryption key and launch an attack. Other examples of abusive interns include DDOS attacks, spam messages, and malicious content hosting. Therefore, customers should check in advance if their cloud provider offers a misuse reporting mechanism. Even though customers are not direct prey to malicious activity, abuse can still lead to service availability and data loss issues.
DoS attacks
Harassment or blackmail-motivated DoS attacks have been around for years. They have gained in importance thanks to cloud computing and are affecting the availability of cloud services. Systems can slow down to a crawl or fail completely. The Australian Bureau of Statistics was also confronted with such a catastrophic failure in 2016 when the agency tried to complete the first national census online. Despite various system tests and stress tests, the census website crashed and went offline the night of the census. No Australian was able to complete his census form. According to CSA, cloud providers tend to handle DoS attacks better than their customers. Protected is anyone who has a plan to mitigate attacks before they occur. This is the only way for administrators to access essential resources when they need them.
Shared Technology Vulnerabilities
Vulnerabilities in a shared technology, including infrastructure, platform, and application, pose a significant threat to cloud computing. If a vulnerability occurs at one level, it affects everyone. If an integral component is compromised, it exposes the entire environment to potential injury. To prevent this, the CSA recommends a deep defense strategy which is known as multifactor authentication.