Growing threats and risks of Cybercrime
Every day, whether at the personal level or at the corporate level, we are exposed to threats from the cyber space. In most cases, we are not even aware of these threats, or even if we acknowledge them, the right decision isn’t made. The global cyber threat situation has never been as unpredictable as in the covid period, which has set a cybercrime as a record year of ransomware and a breakthrough in crypto-currency-miner attacks. Hackers all over the world took advantage of the COVID-19 situation to launch cyber attacks and it took its toll on businesses, organizations, and individuals alike.
Accordingly, companies in all sectors had to contend with serious incidents during this period. The most common causes of critical incidents are the same as last year: targeted attacks (40.7%), malware with critical impact (14%), exploitation of publicly available critical vulnerabilities (13%), and social engineering (5.5%). Targeted attacks in 2021 hit all vertical sectors evaluated in the research except education and mass media, although incidents related to targeted attacks were reported within media organizations. Most human-powered attacks have been identified in government, industrial, IT and financial sectors.
The proportion of serious cybersecurity incidents has increased by half in the past year, from 9% in 2020 to 14% in 2021. This is shown by the research conducted by Kaspersky Managed Detection and Response (MDR). Increasingly complex infrastructures, skill shortages, and increasing sophistication of attacks can impact the efficiency of cybersecurity teams and their ability to detect hostile activity before incidents occur. To gain insight into the current threat landscape, Kaspersky analyzed anonymized customer incidents identified through its MDR service in 2021.
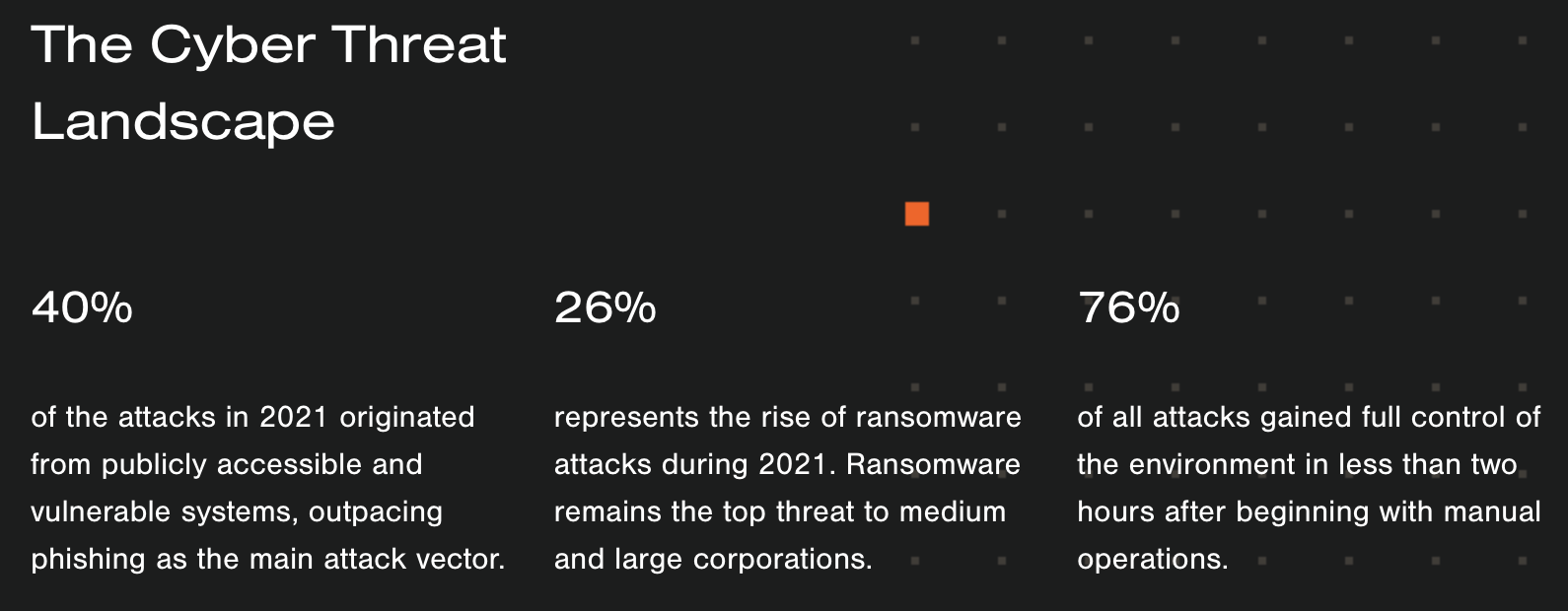
As the ransomware is the fastest growing security threat, known as a moderate or extreme threat by 80% of cybersecurity professionals. Industry experts predicts that, in coming years, this number will continue to increase together with more threats will be added to the known threats. A survey conducted by Veriato Information Security highlighted that Email and web use represent the most common reason of ransomware infection with employees opening malicious email attachments (73%), responding to a phishing email (54%) or visiting a compromised website (28%).
75% of worldwide organizations are touched by ransomware and have experienced up to 5 attacks in the last 12 months alone, 25% experienced 6 or more attacks. The information most at risk from ransomware attacks is financial data (62%)followed by customer information (61%). With such high risk, 59% of organizations are yet not confident at all in their ransomware defence.
CryptoTheft, Microsoft Data Breach, Red Cross Data Breach, PressReader’s, the year 2022 has already been marked by major attacks on a global scale based mainly on a security breach. Today, even if this new wave of malware reveals new patterns of attacks, criminals will remain loyal to the most malicious malware: ransomware, financial data, and digital currency crimes. However, the way these threats are used currently will continuously change into sophisticated way.