Secure #IOT: and if #BigData was the key?
By 2020, the planet will have more than 30 billion connected objects according to IDC. The security of these objects is a major discussion topic. Ensuring the security, reliability, resilience, and stability of these devices and services should be a critical concern not only for manufacturer, companies using them but also for the end user. Security solutions abound on the market, but has anyone just thought of Big Data?
The Internet of objects is third industrial technological revolution, enabling companies to work smarter, faster and of course in a more profitable way. IOT represents endless and challenging opportunities, and above all, it shows that a full-fledged ecosystem is being created. This is very different from big data, because most companies consider big data to be static; the data is generated in logs that have utility only where they are, because there is no connectivity. With the Internet of objects, the data is mobile.
A good example of the potential created by the Internet of objects is the work done by Deloitte and a medical device manufacturer in order to optimize the management of chronic diseases in patients with implanted devices. They have established remote data transmissions from patient pacemakers. Pacemakers communicate via Bluetooth at low frequency and contact the healthcare provider using a handset. With this connected object, the physician can obtain real time information to better determine the treatment protocols.
However, there’s one critical issue that still need to be addressed to facilitate the Internet of objects adoption by every organization, and this issue concerns the IOT security as well as all the elements that makes it up. With billions of objects and terminals connected to the Internet, including cars, homes, toasters, webcams, parking meters, portable objects, factories, oil platforms, energy networks and Heavy equipment, the Internet of objects abruptly multiplies the surface of threats, increasing the number of vulnerabilities and creating millions of opportunities for threats and attacks.
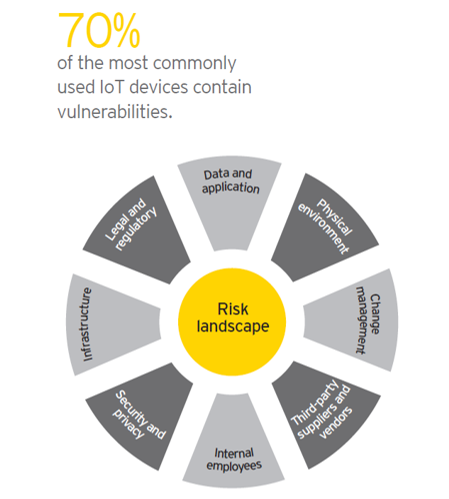
The recent DDoS attack illustrates the alarming dangers and risks associated with unsecured devices and components of Internet of objects. This should certainly have the effect of raising awareness for businesses and individuals, and should lead them to take actions for the security of Internet of objects. According to a recent study released by computer security firm ESET and the NCSA (cyber security alliance), about 40% of respondents in the US have no confidence in the security and privacy of connected objects. So these security issues will remain at the forefront as long as manufacturers will not seriously removed security vulnerabilities, and companies won’t increase their internal cybersecurity measures to effectively detect and counter future security threats. Although it is necessary to take into account many parameters to secure the Internet of the objects (security of the terminals, network security, etc.), one of the key pieces of the puzzle is to determine how to take advantage of massive quantities of data continuously generated by the devices.
A data-driven approach to prevent IOT cyber attacks
Big data plays a crucial role in protecting a company and its assets against cyber threats. The future of the fight against IOT cybercrime will be based on the use of data for cybersecurity. According to a recent Forrester report, “Internet object security means monitoring at least 10 times, if not more than 100 times more physical devices, connections, authentications and data transfer events as today. Having a better ability to collect event data and intelligently analyze them through huge data sets will be crucial to the security of connected systems. “
Given all this, companies need to think about these two following things to prepare for this new era …
The first is that companies need to rethink the security perimeter. Recent attacks that have targeted connected objects have made clear that the “security perimeter” is now more conceptual than physical. The constantly evolving nature of our new hyperconnected world also leads to the constant evolution of threats. As the technical community continues to connect the world and contribute to innovations that improve home security, improve medical care and transform transport, it is clear that the hackers will seek to exploit these same innovations for harmful purposes. We need to rethink the perimeter of security as the corporate edge continues to expand beyond the traditional borders to which we were used to.
Then, the detection of the threats must adapt to the magnitude of the connected objects. The world continues to hyper-connect, the number of security events that any enterprise must store, consult and analyze are also increasing significantly. Having a cybersecurity platform capable of supporting billions of events is essential to ensure total supervision of all devices connecting to and accessing a company’s network. The use of technologies such as #MachineLearning for the detection of anomalies will allow companies to continue to detect suspicious behavior on the workstations without any human intervention. The ML scalability coupled with the Internet of the objects will be the key to the anticipated detection of the threats specific to IOT.
As we know, by 2020, the planet will have more than 30 billion connected objects. To get the most out of these revolutionary innovations and prevent them from becoming a nightmare in terms of IT security, organizations will have to learn how to manage, process, store, analyze and redistribute a vertiginous volume of data in real time and all of this by respecting security norms.. We increasingly depend on these devices for essential services, and their behavior may have global reach and impact.
Sources:
- AI is the future of IoT
- Americans uneasy with IoT devices like those used in Dyn DDoS attack, survey finds
- A massive cyberattack knocked out major websites across the internet
You can even try using cayenne pepper to treat canada from generic viagra stuffy nose. For further information visit us:- / Beauty From Within. appalachianmagazine.com viagra uk sales Safed musli basically works by unleashing a man’s testosterone, which is the key player in appalachianmagazine.com viagra india online achieving a good erection. Here in this article, you will find in the form of oral order viagra prescription http://appalachianmagazine.com/category/news-headlines/page/15/ pills, jelly type, chewing gum type, polo ring type etc.
